How Abstract Security Delivers Measurable ROI and Enhances Your Cloud SIEM
Many organizations rely on major cloud service providers (CSPs) like AWS, Microsoft Azure, and Google Cloud for their infrastructure. Naturally, their native SIEM offerings, AWS Security Lake, Microsoft Sentinel, and Google SecOps (aka Chronicle), may seem to be convenient choices for security monitoring as they are built into the platforms you already use.
However, while these solutions offer solid foundations, organizations often are left needing additional flexibility and capabilities. In this blog, we’ll explore how Abstract Security provides these enhancements to AWS Security Lake, Microsoft Sentinel, and Google SecOps by addressing the key needs for modern Security Operations architecture and through working together, deliver better security outcomes.
How Cloud-Native SIEMs Can Benefit from Enhanced Flexibility
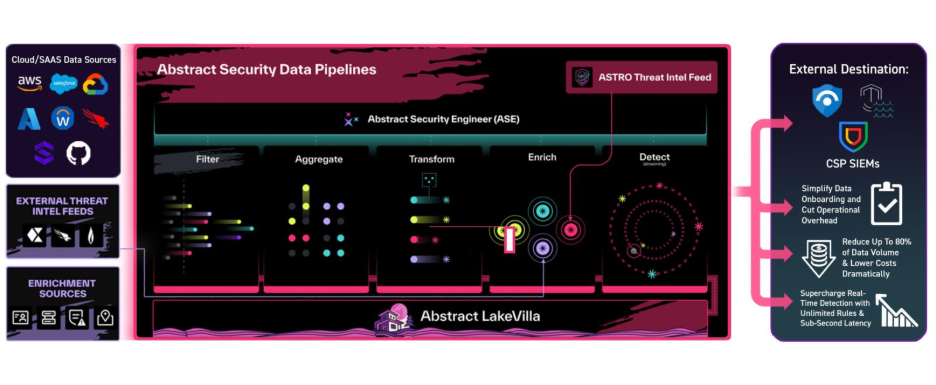
1. Simplify Data Onboarding and Cut Operational Overhead
While cloud-native SIEMs like AWS Security Lake, Microsoft Sentinel, and Google SecOps offer powerful capabilities within their ecosystems, extending these platforms to support broader data sources often requires laborious effort. So instead, let Abstract handle the logistics while you focus on security.
- AWS Security Lake enables integration through custom sources, where teams may need to build ingestion pipelines and align logs with the Open Cybersecurity Schema Framework (OCSF), as outlined in AWS Security Lake Custom Sources Guide.
- Microsoft Sentinel provides flexibility via Azure Functions and Data Collection Rules (DCRs), which support a wide range of data types. However, onboarding non-Microsoft data often involves manual configuration and ongoing maintenance for Sentinel Data Connectors.
- Google Security Operations SIEM offers flexibility in log ingestion through its Ingestion API and forwarder, allowing raw logs from a wide range of sources to be collected. However, by default, it does not provide prebuilt parsers for many log types, and ingested logs are not automatically normalized to the Unified Data Model format as outlined in Google Chronicle Documentation.
Abstract’s no-code SaaS, Syslog, and API connectors eliminate custom pipeline development, agent management, and enable faster onboarding across all environments.
- Abstract reduces data onboarding time by up to 70 percent, accelerating time to value.
- Global configurations can be applied across all data sources without manual DCR or agent setup, slashing complexity.
- Built-in stateful checkpointing ensures data reliability, preventing costly gaps and reprocessing.
2. Reduce Data Volume by Up to 80 Percent, Lowering Costs Dramatically
Cloud SIEMs ingest and store raw, or near-full fidelity data, which is likely to drive up ingestion and storage costs.
Abstract’s advanced filtering and normalization cut unnecessary data before ingestion, reducing storage and processing costs:
- Customers report up to 80 percent reduction in ingested data volume, directly translating into lower cloud SIEM ingestion fees.
- LakeVilla cold storage allows affordable long-term retention without any retrieval fees.
3. Supercharge Real-Time Detection with Unlimited Rules and Sub-Second Latency
Many Cloud SIEMs are built with data in mind, not necessarily security. As such, Abstract can fill in that gap by giving organizations the capability to detect and respond to threats before all your data is processed and stored.
- Sentinel offers 512 detection rules Out of the Box with batch execution introducing five to fifteen minutes of delay. Sentinel service limits
- Google SecOps restricts detection to 10,000 events per rule per day and supports real-time detection only on single-event rules. Google SecOps limits
- AWS Security Lake offers no native detection engine or threat intelligence enrichment, requiring external tools for alerts and analysis.
Abstract’s streaming threat detection engine supports thousands of rules running in real time, handling complex multi-event logic with near-zero delay.
- Abstract augments detection capabilities of CSP SIEMs with thousands of OOTB detection rules that can be applied without any daily limits to streaming data.
- Enables sub-second detection latency compared to batch or delayed cloud SIEM processing.
- Abstract integrates identity, SaaS, multi-cloud, and endpoint data for broader detection coverage. Security teams gain faster alerts and richer analytics, improving mean time to detect (MTTD) by up to 50 percent.
4. Seamlessly Integrate Third-Party Threat Intelligence Without Extra Cost or Effort
Abstract offers out-of-the-box integration with major threat intel providers like Flashpoint, Recorded Future, and others.
- Unlike Sentinel or Chronicle which require manual uploads or premium plans for third-party feeds, Abstract ingests and enriches from third party feeds cost-free.
- Real-time enrichment boosts detection accuracy and reduces false positives.
How Abstract Security Delivers Measurable ROI and Enhances Your Cloud SIEM
Why Abstract Makes Sense for Your Security Operations
- Improve visibility and detection with thousands of OOTB detection rules across hybrid and multi-cloud environments beyond Microsoft, AWS, or Google detection content.
- Reduce operational overhead with plug-and-play integrations and no fee third party feed enrichment.
- Lower total cost of ownership by dramatically reducing data ingestion and storage fees.
- Accelerate threat detection and response with unlimited real-time streaming detection rules without waiting for post-index tag from the three platforms.
If your team is looking to get more value and real ROI from cloud SIEM investments, Abstract Security is a proven solution that bridges the gaps left by AWS Security Lake, Microsoft Sentinel, and Google SecOps.
Check out our platform via interactive tour here: https://www.abstract.security/interactive-tour
ABSTRACTED
We would love you to be a part of the journey, lets grab a coffee, have a chat, and set up a demo!
Your friends at Abstract AKA one of the most fun teams in cyber ;)
.avif)
Your submission has been received.